
What is IDM? What’s on with IDM?
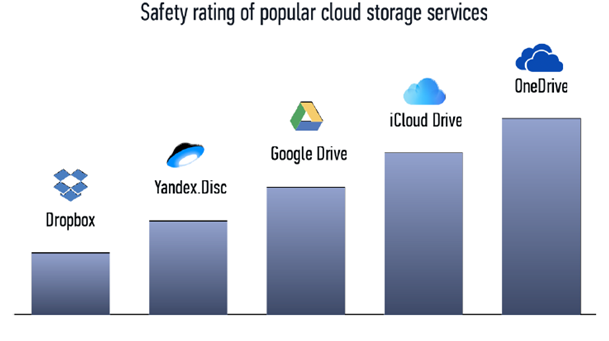
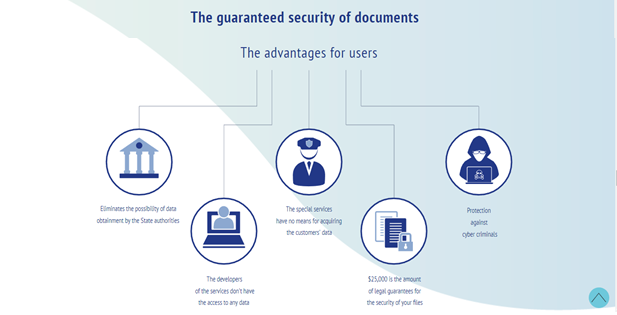
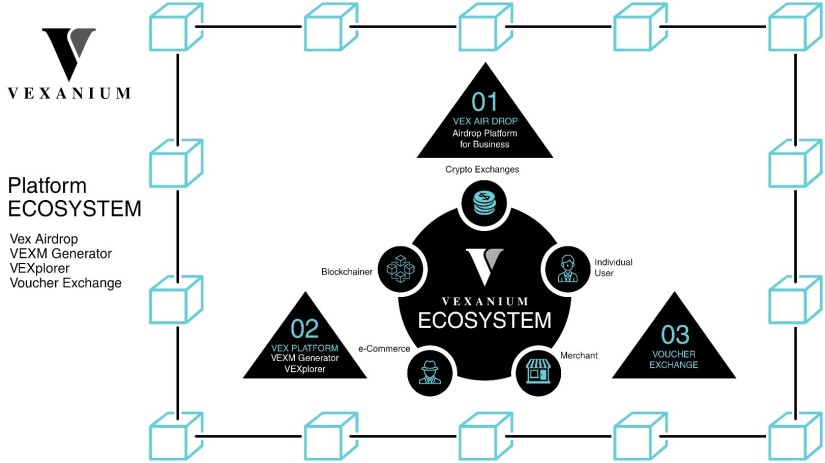
IDM has its own patented data protection technology called SIZE and is preparing to launch a new service – a global decentralized ecosystem that connects users who want to store information safely and miners who provide memory on their devices to generate income. Our development team has created a working prototype of a cloud storage service called BoobookBox. The service was launched in 2015 and has more than 2 thousand active users. The working prototype was launched to test the technology, both by developers and third-party organizations. IDM can successfully compete with all cloud data storage services, as it offers following exclusive features: o The most safe and secure data storage system and data transmission o Affordable price o The only player on the market offering this level of data protection o Savvy marketing strategy o Legal guarantee on data security IDM focuses on strictly defined segments of the consumer and business market, and takes advantage of a competitive market opportunity, namely the demand for secure data storage.
IDM can successfully compete with all cloud data storage services, as it offers following
exclusive features:
o The most safe and secure data storage system and data transmission
o Affordable price
o The only player on the market offering this level of data protection
o Savvy marketing strategy
o Legal guarantee on data security
IDM focuses on strictly defined segments of the consumer and business market, and takes advantage of a competitive market opportunity, namely the demand for secure data storage.
there are so many flaws and problems in Internet-based storage, one of the difficulties in accessing information that allows access by others. such as the secret files from SONY that have been hacked and published by hackers. of course this is very worrying to many parties. now present IDM (Ideal Data Memory). this project provides various features that can help you in maintaining and storing your data, either based on computer or internet. There are many problems again that always happen in millennial and of course IDM will solve them. See below!
Current Trends And Issues Associated With Cloud Data Storage
The 21st century is the age of information. More and more data are generated on daily basis creating an ever-increasing demand for storage space. Not every home
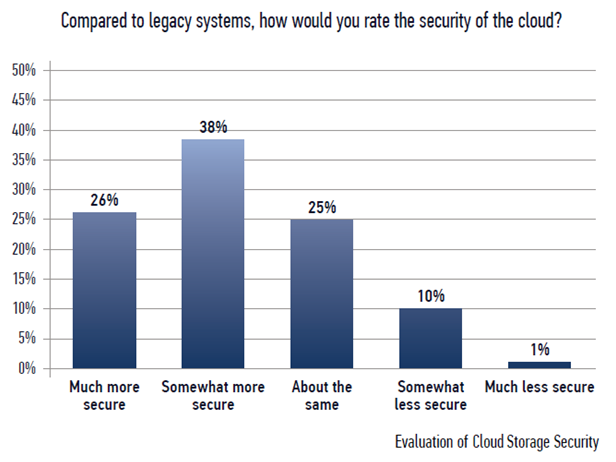
computer, let alone a mobile device, can store all of its own generated data. The capacity of the built-in memory is growing along with requirements for data safety. The increased volume of generated data proportionally increases the number of potential threats to the storage of this data. With the growth in the number of devices, cloud storage services are becoming increasingly important. Many cloud storage providers promise fast, reliable and convenient services. However, the reality is a bit more complicated. What kind of threats to the information are the most relevant today? Evaluation of Cloud Storage Security.
Pure Statistics
o The year 2013 was marked by a scandal involving the outdated SSL service certificate by Microsoft Azure, which provided criminals with an opportunity to hack the Xbox Live system;
o The so-called Celebgate incident, which happened in 2015, when hackers stole intimate photos of celebrities from the iCloud (Apple) cloud storage;
o The number of hacks inflicted on cloud services is growing every year at the rate
around 50%;
o Approximately 70% of companies have at least one application running in a cloud;
o Lloyd’s of London and Cyence believe that a massive attack on cloud storage can
cause losses in excess of $ 5 billion, and only 15-17% of the total amount will be covered by insurance;
o In 2017, the data storage of Equifax, the US leading consumer credit report agency, had been hacked resulting a personal data loss of 143 million customers. Consequently, the value of company’s stocks has plummeted by 13%;
o The absence of two-factor authentication resulted in a personal data theft of 80 million customers of Anthem, an American health insurance company.
Data Loss In Cloud Storage
Despite the fact that this type of storage is called “cloud”, the data is stored in physical terrestrial and underground locations, called data centres. The actual storage devices are hard disks prone to various effects similar to those inherent in modern HDDs, such as an appearance of bad sectors, errors caused by voltage drops or physical damage to the disk surface, both due to improper operation or a design defect. As a rule, all information is duplicated in backup copies according to a specific schedule. However, this method does not fully guarantee the safety of your data. Also we must consider the human factor.
Theft Of Data From Cloud Storage
Data is not always lost as a result of technical failures. Often there is a banal theft. The criminals may steal information just for fun or with the purpose of honing their hacking skills. Information can be stolen with a very specific purpose: to make money through blackmailing or selling valuable data to interested parties. Not long ago, the media was buzzing with the news regarding the theft of intimate photos of celebrities from the cloud storage belonging to one of the main players on the mobile market.
After the scandal, the company responsible for security of the storage, as a third-party contractor, left the market, but the pictures, however, went all over the world.
Network Attack
The storage where your data is located may be subjected to a targeted cyberattack. In that case, you could be just a casual victim, especially if the hackers aimed at the entire service with the purpose of stealing or damaging the personal data of a particular user, whether it be an individual or a company.
Ddos Attack
No matter how safe cloud storage is a simple DDoS attack can cause huge losses to the service by slowing down or blocking its operations, with users not being able to retrieve their data or use the service.
Human Factor
Despite the abundance of cyberthreats, the so-called human factor remains the most dangerous element in the process of securing data. An attacker can be located within the data centre, for example, as a system administrator. This situation is quite common. Some employees are willing to commit crimes to enrich themselves. The stolen personal data or the access to that information can be sold to various criminal organizations that may inflict an enormous damage, both moral and material.
Countermeasures To Emerging Threats
- The encryption of data by the user could be a viable method of countering cyberattacks and potential data theft;
- Another way is to select an additional option offered by cloud service, which provides uploaded data to be encrypted by the service;
- The two-factor authentication (2FA) allows to increase the level of data access protection with minimum costs;
- Anti-virus software that is a more conservative method of data protection.
How To Secure The Information In The “Transparent” Cloud.
Almost all existing on the market cloud storage services guarantee the integrity and maximum protection of user information from external influence of third parties. Nevertheless, all services, one way or another, are obliged to comply with legal requirements of the country in which they provide services. Even the use of the AES256 encryption protocol, adopted as a data protection standard by US governmental organizations, does not guarantee the protection of your information. According to the current legal practice, a service is required, as per legislation of most countries, to provide government authorities with access to user data upon request.
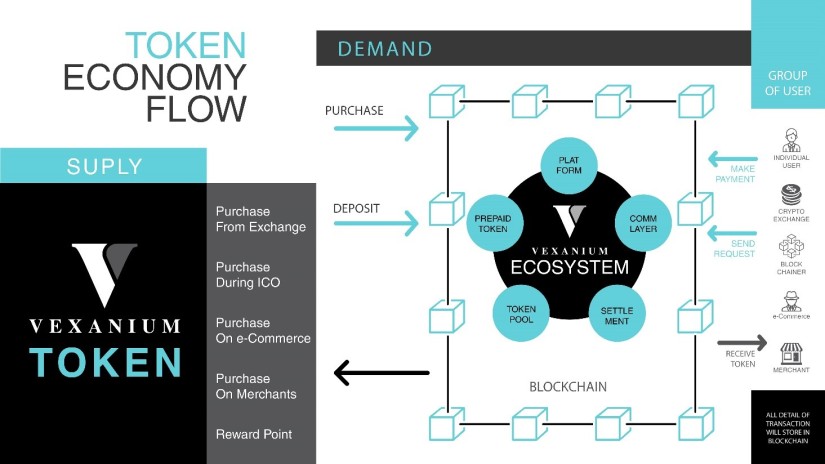
From those explanation, IDM will solve them, IDM service provides a decentralised distributed cloud data storage system where security against both loss and theft of data provided by unique algorithm SIZE.
To procure the distributed data storage, the service will rent a free memory from miners for a reward. The miners all over the world would be able to lease memory on their devices, including devices morally and technically obsolete (old smartphones, dated hard disks) and receive a continuous remuneration.
Our patented algorithm SIZE supports an excellent protection of a file from loss
(corruption) and can guarantee a file recovery from only 2% of the remaining data. Administration of the service will be managed by blockchain technology.
JOIN US,
WEBSITE : https://myidm.io/
TELEGRAM GROUP: https://t.me/idmprotect_en
ANN THREAD : https://bitcointalk.org/index.php?topic=3395543.msg35555064#msg35555064
TWITTER : https://twitter.com/IDMdatasecurity
MY BITCOINTALK PROFILE : https://bitcointalk.org/index.php?action=profile;u=1346920



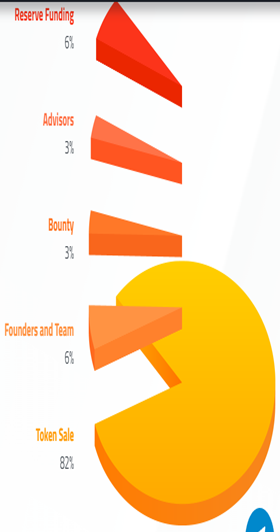
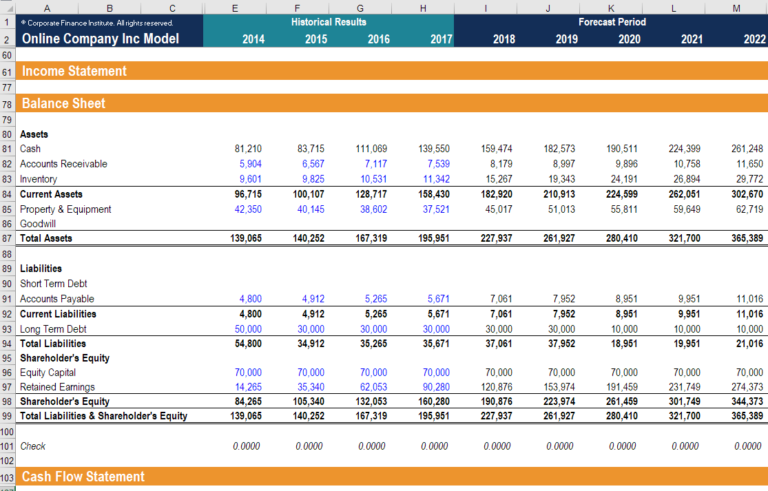


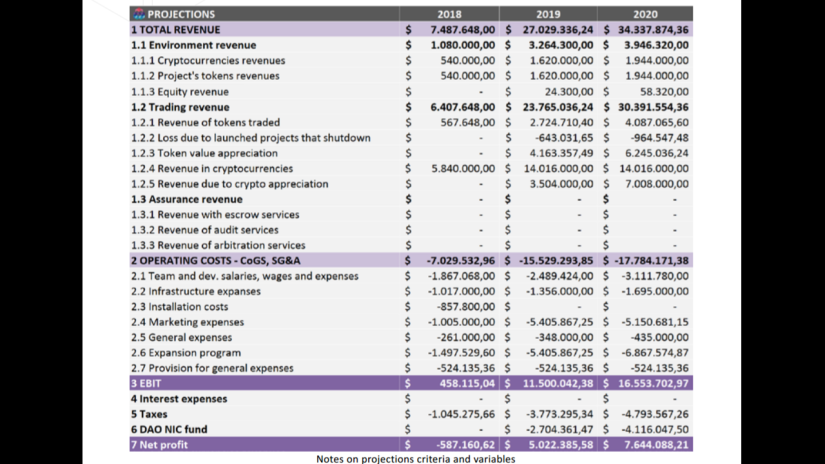 ICONIC financial model
ICONIC financial model





